Accessing local-network-only web pages from outside the firewall
VPNs aren’t as painless as they ought to be, and setting one up purely in order to get at web pages that have been hidden behind a firewall can seem to be overkill sometimes. But then, there are good reasons for hiding things like internal finance-and-admin web pages behind a firewall. What to do?
OpenSSH to the rescue! Greg Tourte just pointed out an alternative to using the VPN in order to access these internal web pages, such as Agresso. It certainly works on Linux and on the Mac, and should also work using Putty (see http://home.fnal.gov/~dwd/ssh-to-browse-behind-firewall.html). This is pretty useful. For example, people within UKOLN who might be having difficulty accessing internal web pages such as Agresso due to VPN problems should be able to use this method instead.
It relies on the fact that OpenSSH has a lot of little-known functionality, in this case, the ability to act as a SOCKS proxy (see http://en.wikipedia.org/wiki/SOCKS for lengthy and boring introduction). In short, OpenSSH can tunnel through to a machine at UKOLN and then allow the browser to treat that connection as a standard web proxy. Because the web proxy endpoint is inside the Bath network, it permits access to internal web pages.
Here is a blog post describing the basics of this openssh functionality:
http://alien.slackbook.org/blog/securely-browsing-the-net-using-socks/
Here are the steps required to set up a SOCKS proxy in order to access these internal web pages remotely (we just tested this on a Mac and on Linux).
1. Install Foxyproxy on Firefox : https://addons.mozilla.org/en-US/firefox/addon/2464
2. Open a terminal window and type: ssh -D 8888 yourusername@InternalServer.YourUniversity.ac.uk
Type in your password when prompted to do so. You will then get a ssh session on InternalServer; just leave this open.
3. Open FoxyProxy, and complete the following steps:
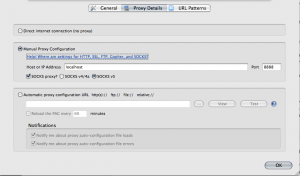
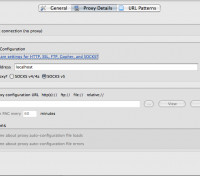
a) add a new manually configured proxy, with the host/IP ‘localhost’, port 8888, click ‘SOCKS proxy?’ and set it to SOCKS v5.
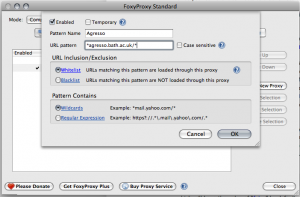
b) Add a new pattern defining when this proxy should be used:
Given the example of setting this up for Bath’s Agresso server:
Call the pattern something like ‘Agresso’, and put in the URL: *agresso.bath.ac.uk/*
Under ‘URL Inclusion/Exclusion’, select ‘Whitelist’, and under ‘Pattern Contains’, select ‘Wildcards’
Make sure that the newly set up proxy is enabled.
4. Type http://agresso.bath.ac.uk/ into the address bar. Hopefully, FoxyProxy should make use of the pattern that we have just set up and send the traffic through via the SOCKS proxy.
Caveats: Obviously, just as you need to turn on the VPN before you can access Agresso via the VPN, you will also need to run the SSH step before you can access Agresso via SSH – the SOCKS proxy only lasts for as long as the SSH session remains connected. That said, you can simplify the setup process by adding it to your ~/.ssh/config file, for example:
Host agresso
HostName InternalServer.YourUniversity.ac.uk
DynamicForward 8888
User MyUsername
If I then type ‘ssh agresso’, and type in my password, that does the trick.
This simply goes one step closer to proving that no matter what the problem, if it involves a network, SSH has an answer.